What is DPN?
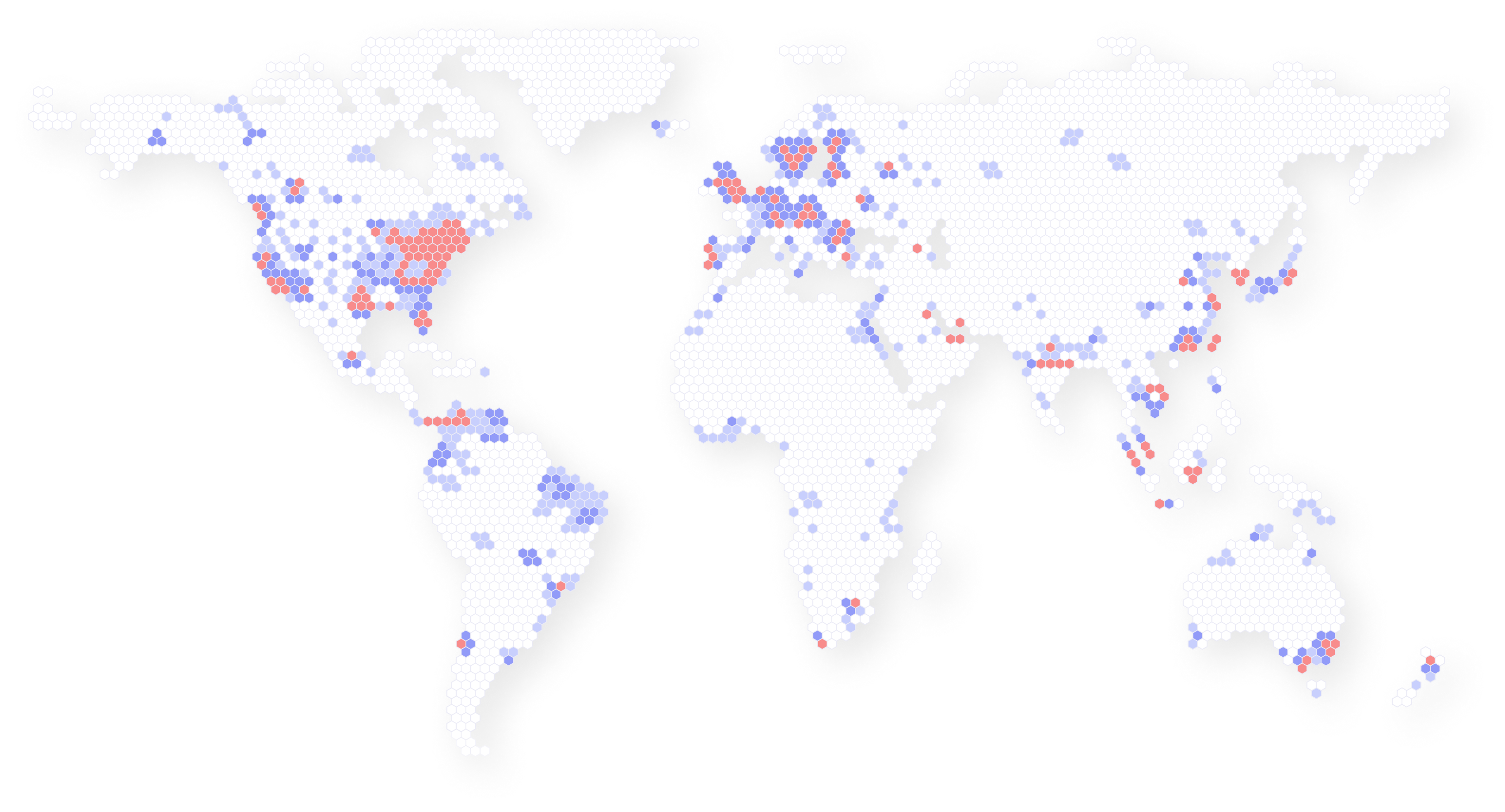
Unlike traditional VPNs that route users through central servers, the Decentralized Private Network (DPN) uses over 200,000 global nodes, offering stronger privacy, true anonymity, and freedom from censorship.To learn more about DPN, please refer to this article "A 101 on DPN".
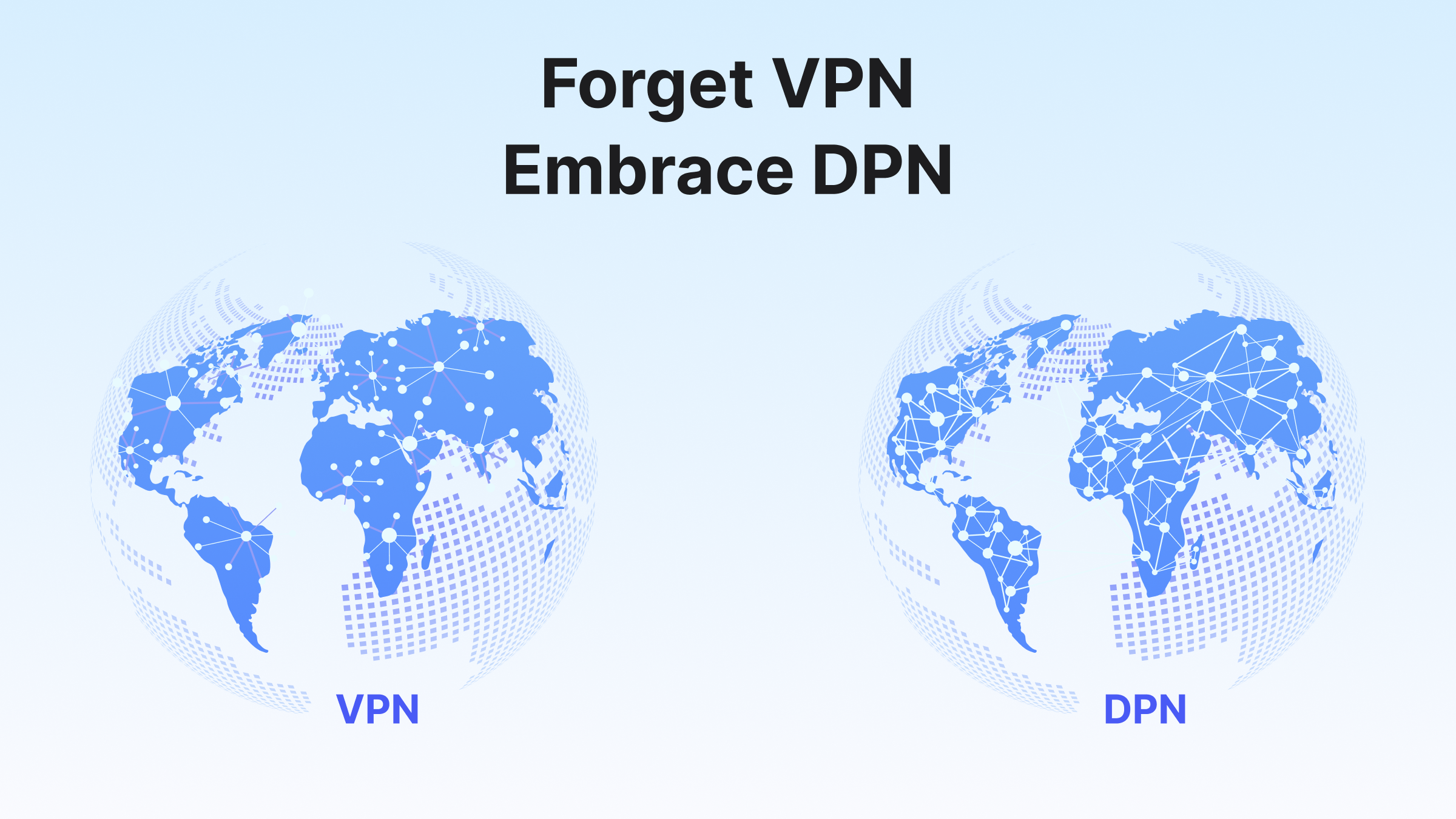
DPN vs. Traditional VPNs
Not all security solutions are created equal. See how Deeper Connect’s DPN (Decentralized Private Network) differs from typical centralized VPNs.Protect Your Entire Network with One Device
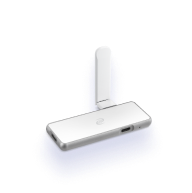
Deeper Connect provides a secure gateway that protects all your IoT devices. An all-in-one device requiring no additional fees for a more private and secure internet.

Plug-and-Play Protection
Easy setup even for the tech novice.
Security & Privacy
Lifetime DPN
Product
Deeper Connect is the world's first decentralized hardware VPN — a powerful all-in-one device delivering enterprise-grade cybersecurity, privacy protection, and Web3 mining capabilities.
Why Choose Deeper Connect?
End-to-end encryption and open access tunneling keeps your online activities secure and private.
More Than Just a VPN
Deeper Network goes beyond just privacy protection with its built-in cyber-security that safeguards your internet.
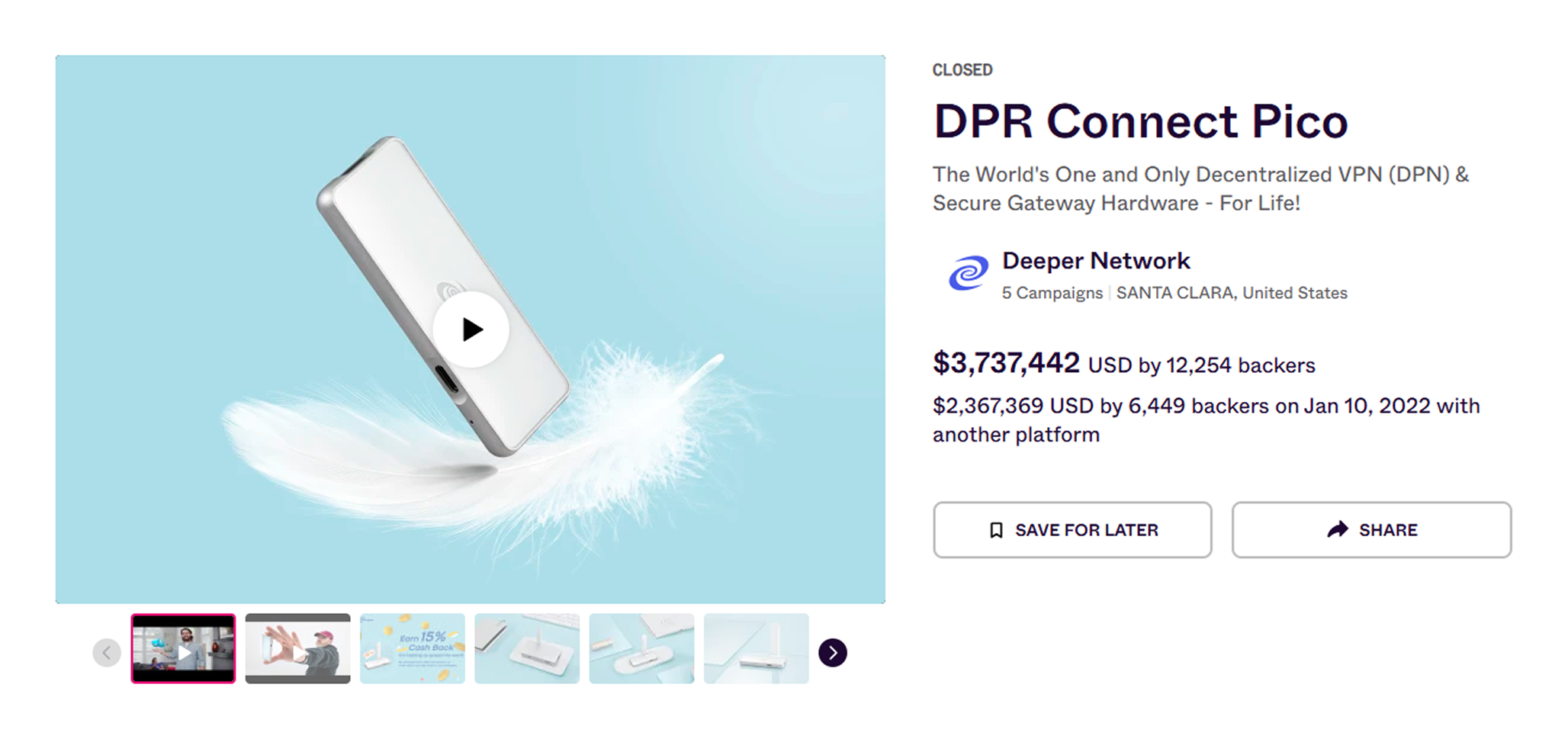
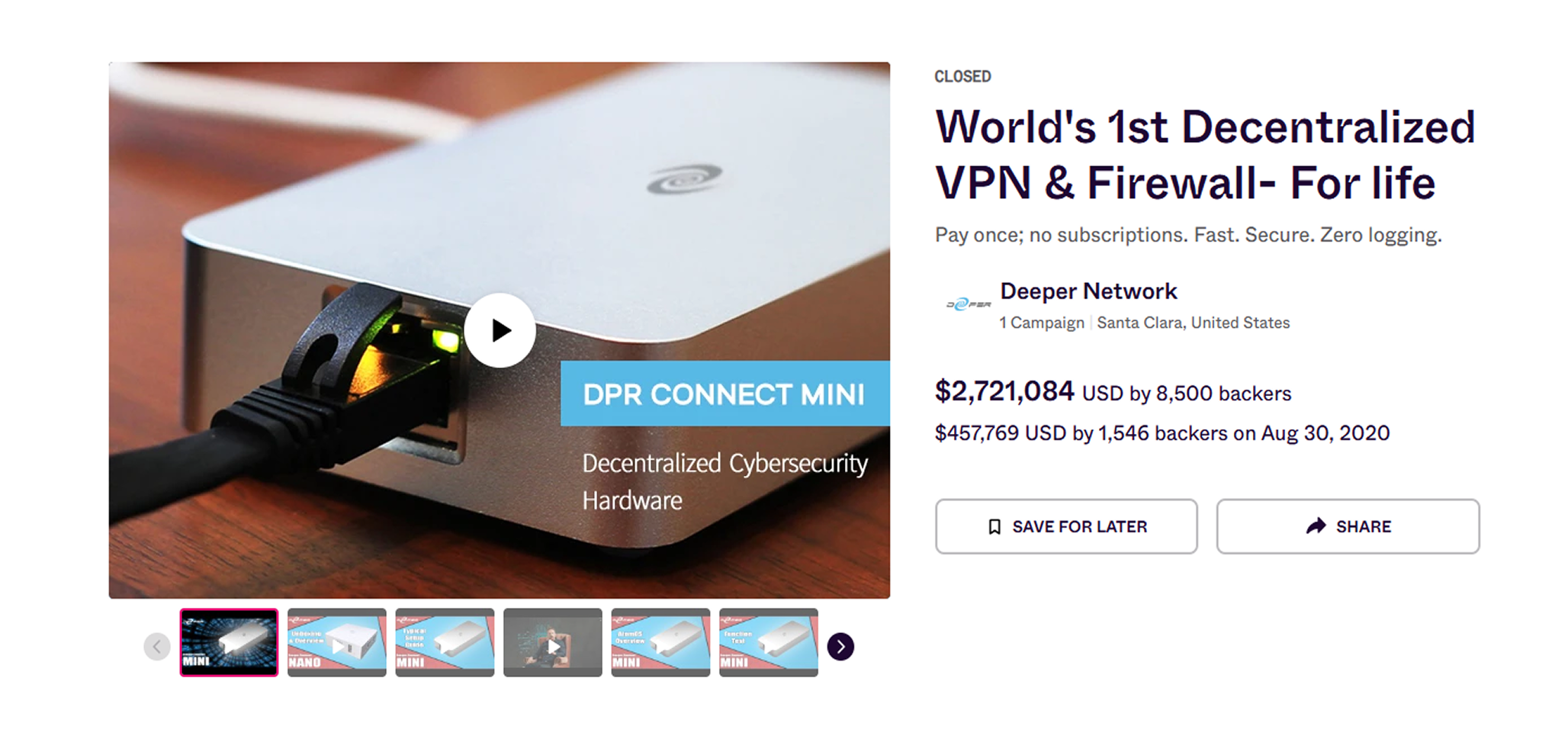
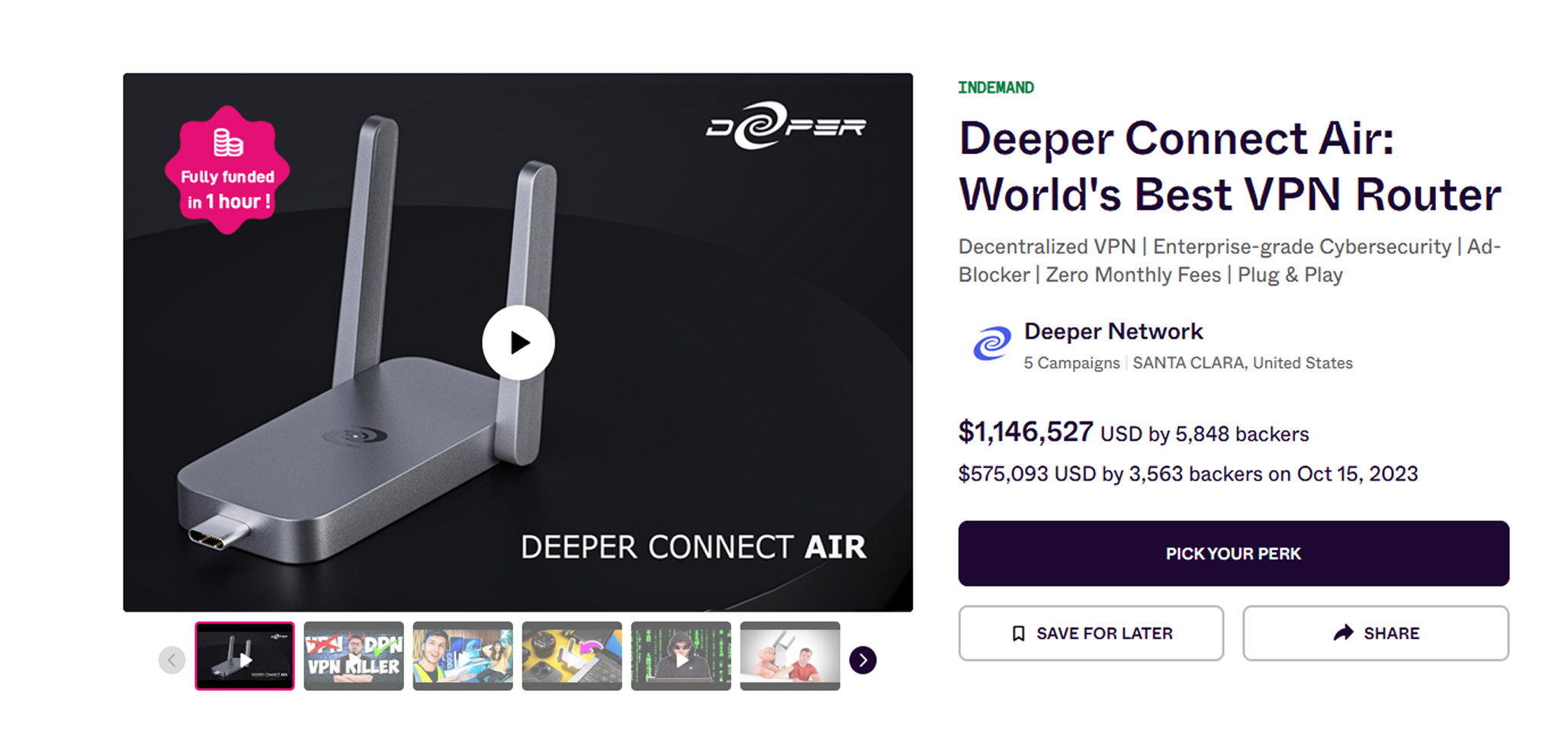
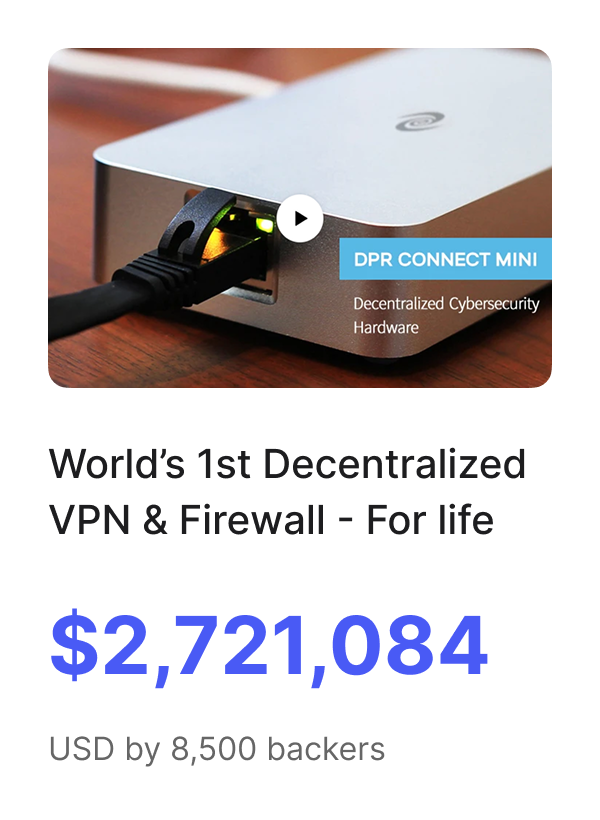
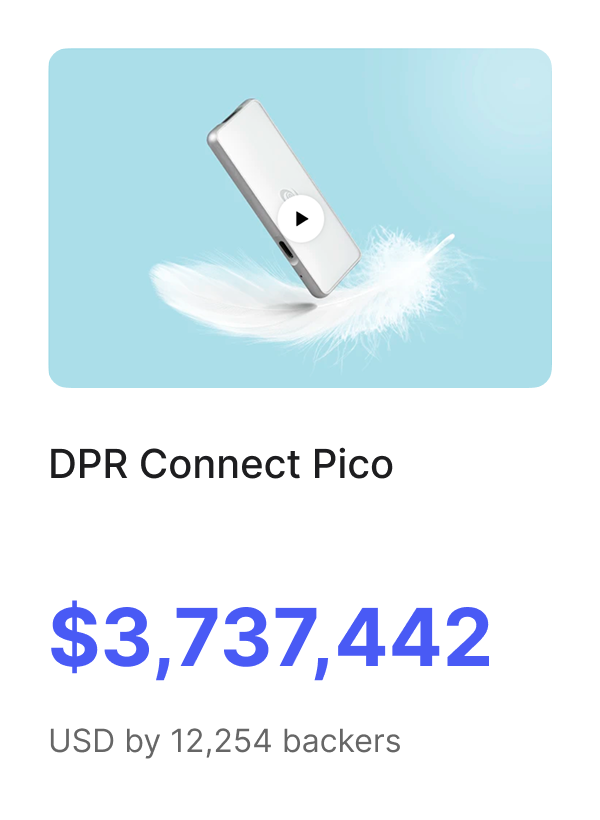
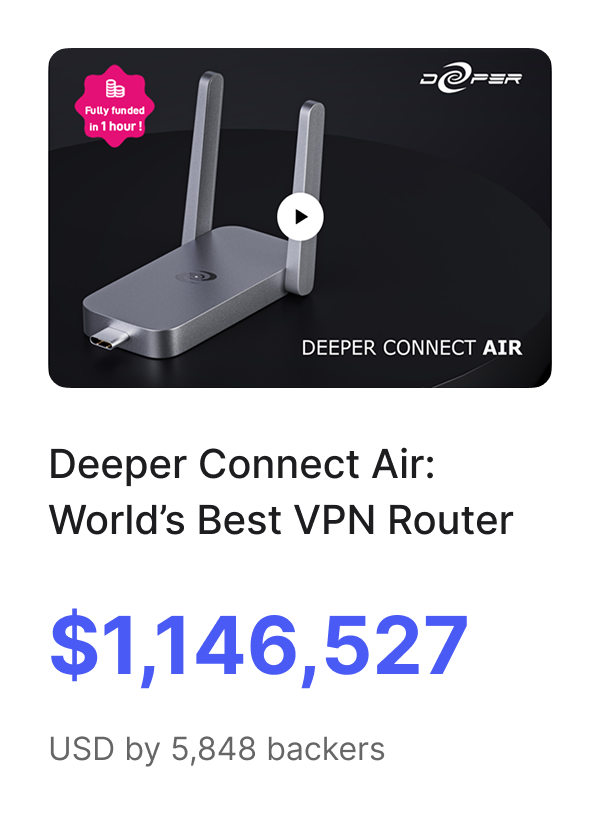
Top 3 Crowdfunding Success
Our top three campaigns—Deeper Connect Mini, Pico, and Air—exceeded expectations by raising millions from tens of thousands of backers.
AtomOS: Your All-in-One Network Management
Take full control of your network with AtomOS, a powerful and intuitive management dashboard.

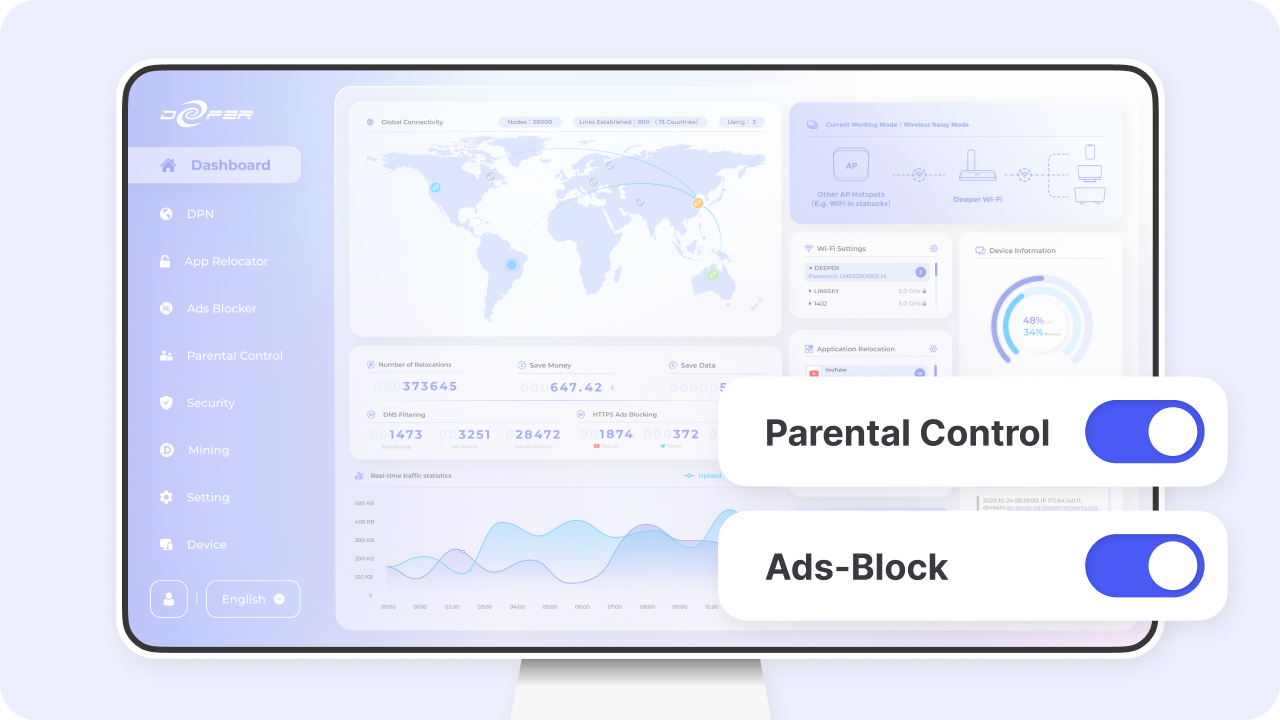
Lock-free OS – The Atom OS dashboard gives users a user friendly UI to monitor and manage your device and network.
Custom Security – Fine-tune protections with Blacklist/Whitelist and HTTPS blocking.
App Relocator – Route specific apps through different regions for better performance and access.
Received Numerous international Accolades



 X
X